Frequently Asked Questions
What equipment needs to be installed?
What are the installation steps?
How much bandwidth do I need to stream Netflix?
Why can I not get web pages or email?
Why is my WiFi signal low and the connection keeps dropping?
How do I fix WiFi security for iOS 14 Weak Security?
How do I tell if an email is a Phishing or Scam email?
What equipment needs to be installed?
A wireless internet receiver needs to be installed on the exterior of your house. A power supply unit (POE Injector) needs to be installed inside the house in close proximity to an electrical outlet. A cabled needs to be installed between the internet receiver and the power supply unit (POE Injector).
What are the installation steps?
Our install technician will visit your location to determine if there is a spot on the exterior of your house that has clear line of sight to our tower. Next the technician will test to see if there is adequate wireless signal for reliable performance. If the signal is adequate, the technician will mount the wireless internet receiver unit to the exterior of your house. From the receiver unit, a network data cable will be run to the interior of your house to a room of your choice. The network cable plugs into the power supply unit (POE Injector) thus powering up the receiver unit. The install technician will supply another network cable that also plugs into the POE Injector. The install technician will plug in this second network cable into a laptop computer and test the internet connection performance. At that point, the technician will pass the network cable to the end user so that they may plug the cable into a computer or into a WiFi router.
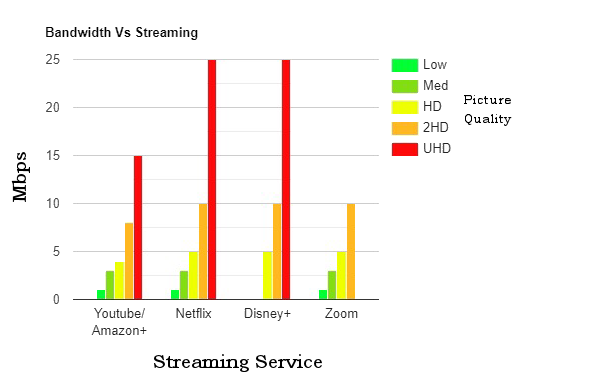
How much bandwidth do I need to stream Netflix?
Below is a chart that shows how much bandwidth you need to stream content from various streaming providers at various
levels of picture quality.
Why can I not get web pages or email?
There are several possible reasons why you may not be able to access the Internet:
If your computer has not been rebooted for a while you may be prevented from accessing the Internet. This occurs because your computer's resources have been depleted from opening and closing programs. Simply close your programs and turn your computer off and back on.
If you have your Internet connection going through a router, try cycling the power to the router.
Try cycling the power to the Internet receiver. Wait for at least 2 minutes for the Internet receiver to boot up before trying to connect.
Make sure you have all of the cabling plugged in correctly. Check to see that the link light for each network cable is lit.
Sometimes, people mistakenly disable their Local Area Connection. Go to the Network Sharing Center and make sure the LAN connection is enabled.
Make sure your account is not past due.
We do perform periodic maintenance and upgrades to our system which can cause services to be temporarily unavailable to you. Normally, we will contact you via email at least 24 hours before a scheduled maintenance or upgrade.
On rare occasions, we may be having problems with our equipment. We do monitor our system and will address any unscheduled system outages as quickly as possible.
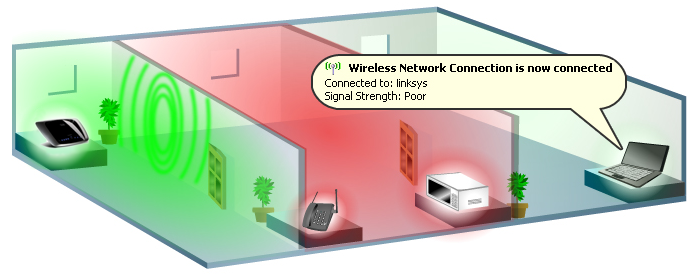
Why is my WiFi signal low and the connection keeps dropping?
There are a few factors why your wireless device is getting low or poor signal from your router.
Low or poor signal is mainly caused by five (5) major factors:
- Distance problems.
- Physical obstructions.
- Wireless interference.
- Outdated firmware.
- Power outage.
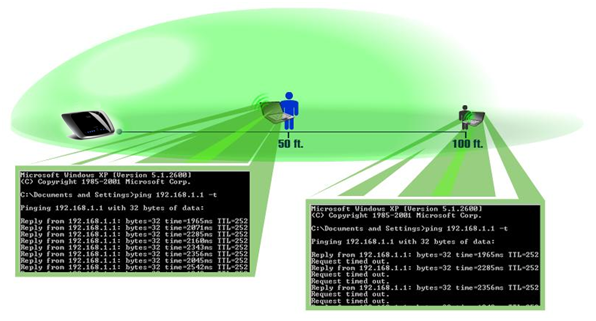
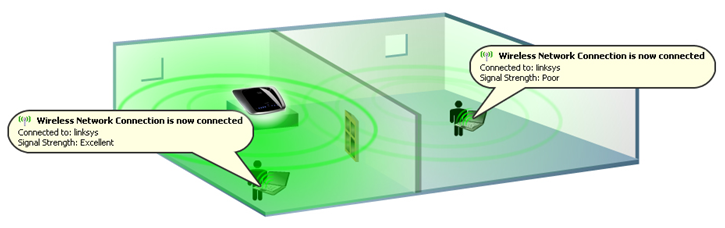
Wireless devices have limitations when it comes to their signal range. For devices running on 2.4 GHz, the range can go up to 100-150 feet (30-46 meters). If your wireless network devices are too far from each other, consider relocating the devices. Remember that distance is directly proportional to signal strength. The farther you are from the wireless router, the weaker the signal. To check if you’re getting a stable connection, perform a continuous ping. If you’re getting replies all of the time, this means the connection is stable. If time outs are occurring frequently, the connection is not that stable.
To get the best connection, you may need to find ways to move your WiFi devices closer to the center of the router’s range. When choosing an area where the router will be placed, ensure that it is well ventilated and not in direct sunlight. Try to place your router in close proximity to where you will use your wireless devices. For example: If you mainly use your wireless devices on the top floor of your house, installing the router in the basement would not be ideal.
Physical obstructions
Wireless networks are also susceptible to obstructions that may lead to low signal.
Oftentimes, the signal gets reflected, refracted, or absorbed by the obstruction.
Common obstructions are:
- Cabinets or drawers.
- Mirrors, Glasses.
- Metal Objects.
- Floors, walls, and ceilings.
- Aquariums.
Routers have a default broadcast range that is dependent on their wireless networking
standard (Wireless -B, -A, -G, -N, -AC draft) and the wireless signals broadcasted by
the router may not be able to completely penetrate thick walls and other common obstructions.
Also, some routers have an optional range extender to boost the signal of your router if you
have a big area and there are a lot of obstructions between your router and the wireless device.
Wireless interference
Common sources of interference are:
- Neighboring wireless networks.
- Microwave ovens.
- 2.4 GHz cordless telephones.
- Bluetooth devices.
- Wireless baby monitors.
Outdated firmware on the router
Outdated firmware on the router can sometimes cause connection and performance issues in your network. To fix this, you need to upgrade the firmware of your router.
NOTE: Instructions for upgrading the firmware will vary depending on your router model.
Power outage
One factor that may also trigger the poor performance or loss of wireless signals coming from the router would be power/electricity interruptions. If you are not able to acquire any wireless signal after a power outage, you may powercycle the router by unplugging and re-plugging the power cord from the power outlet for 10 seconds. However, if the powercycle still does not resolve the problem, you may need to reconfigure the wireless settings of your router.
NOTE: Instructions for reconfiguration will vary depending on your router model.
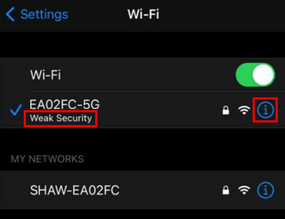
How do I fix WiFi security for iOS 14 Weak Security?
Weak Security error
-highlight.png)
Apple released the iOS 14 update that flags any WiFi router as "Weak Security" while using older WiFi security settings (WEP, WPA, WPA2 TKIP or WPA2 TKIP+AES).
NOTE: Not all routers or other devices support WPA2 (AES) and they may need to be updated or replaced, or you can leave the settings as they are with the “Weak Security” message on any Apple devices running iOS 14.
For more information about the Apple update, read About Apple iOS 14 Updates, and/or Recommended settings for Wi-Fi routers and access points
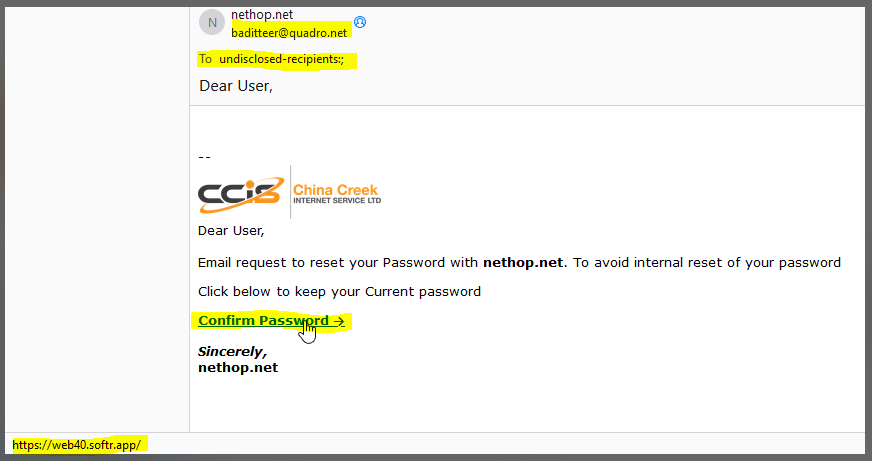
How do I tell if an email is a Phishing or Scam email?
In our interconnected digital world, email has become an essential tool for communication and business transactions. However, it has also given rise to a prevalent cyber threat known as phishing. Phishing emails are deceptive messages designed to trick recipients into revealing sensitive information, downloading malicious attachments, or clicking on malicious links. Let's delve into what phishing emails are and provide you with effective methods to detect and defend against them.
Understanding Phishing Emails:
Phishing emails are crafted to appear genuine, often mimicking the branding, language, and style of legitimate organizations. Cybercriminals use various psychological tactics to manipulate recipients into taking actions that compromise their security. These actions could include:
- Clicking on Malicious Links: These links may direct you to fake websites that closely resemble legitimate ones. Once there, you might be prompted to enter personal information like passwords, credit card details, or Social Security numbers.
- Downloading Malware: Attachments in phishing emails could contain malware designed to infect your device. Opening such attachments can lead to data breaches, identity theft, or even control of your device by malicious actors.
- Impersonating Trusted Entities: Phishers often pose as well-known companies, government agencies, or financial institutions. They might claim that your account has been compromised or that you need to update your information urgently.
Detecting Phishing Emails:
Fortunately, there are several ways to spot phishing emails and protect yourself from falling victim to their traps:- Check the Sender's Email Address: Hover over the sender's name to view their actual email address. Be wary of misspellings, strange domains, or email addresses that don't match the official domain of the organization they claim to represent.
- Inspect URLs: Hover your mouse cursor over links without clicking them to preview the actual URL. Be cautious of shortened links or URLs that don't match the legitimate website's domain.
- Look for Generic Greetings: Phishing emails often use generic greetings like "Dear Customer" or "Dear User" instead of addressing you by name.
- Urgent or Threatening Language: Be suspicious of emails that create a sense of urgency, pressure you to take immediate action, or threaten dire consequences if you don't comply.
- Check for Spelling and Grammar Errors: Many phishing emails contain noticeable language mistakes. These errors can be a red flag indicating an illegitimate source.
- Verify Requests for Personal Information: Legitimate organizations seldom request sensitive information via email. If in doubt, contact the organization directly using official contact information from their official website.
- Inspect to whom the email is sent to: If you see that the email is sent to " undisclosed-recipients " then that is almost a certain give away that it is a Phishing email.
Defending Against Phishing:
To bolster your defenses against phishing attacks, consider these recommendations:- Educate Yourself: Learn how to spot Phishing emails using the methods we discussed above. Stay informed about common phishing tactics and be cautious when interacting with unexpected emails, especially those requesting personal information or password reset requests.
- Use Security Software: Install reputable antivirus and anti-malware software to protect your devices from potential threats.
- Enable Multi-Factor Authentication (MFA): MFA adds an extra layer of security by requiring a second form of verification in addition to your password.
- Regularly Update Software: Keep your operating system, web browsers, and email clients up to date to ensure you're protected against known vulnerabilities.
Below is an example of a Phishing Email: